Revelations About the Thapar WiFi, and the Utilities Regarding Them! [EACCESS, TU, LC, etc]
Sup fellas! Doing good? Hope so! So finally I have decided to write this article, after procrastinating a lot (Thank you my inner self) and thinking about this a lot.
So what is this about?
Have you ever used the Thapar Wifi and wondered about the inner workings of this mass deployed wireless infrastructure? Well, that is what this article is about! Getting you to know the “DARK” secrets of these wifis and letting you exploit them to your advantage :).!
Revelation 1: We are all connected.
We are, really! So basically what this means is, that everyone using Thapar Wifi, is all connected through local LAN networks! It is quite simple and many would say that they already know this simple fact but guess what? they still haven’t used or exploited this!
How can you use this? (Gimme some use case bish)
- Gaming, bruh like really. if your game supports local LAN play, you can just create a server and have your friends play through thapar inter-lan systems!
The benefits? Near 0 ping with no network throttle.
I have personally used this to play games like CSGO and Minecraft with my friends! A very great experience. - Hosting Development Servers, might not be relatable to most non-tech users but this means that rather than hosting on a separate server like Heroku, GCP, etc You can host your applications (like Django-app, Node+express app, or just APIs) and give thapar local ip (starting with 172.x.x.x) to other’s connected to Thapar Wifi as well, and they can use your IP to access services or see your deployed application without you trying to host the server globally on some 3rd party platforms (mentioned above, like Heroku)!
- A Thapar Network-Specific Only App, Imagine you want to create some application/service/etc that is only usable on Thapar Wifi, Anyone outside cannot access it and anyone connected to it can use it! You can exploit the local access connection of these Wifi’s to implement it!
- File Transfer, I know it might seem stupid to have a whole separate point on this but thought this was important. So basically we could have one person host a temporary file hosting server (Using point 3) and give their IP to others that want to download your file, the others on the network can use this IP to access files shared by User 1, and hence download it!
The gist of it is over, Scroll to Revelation 2 or Continue reading for some examples/my thoughts!
Some Examples:
File transfer: (Using python for quick hosting)
How to? Cd to your bucket directory and run:
python3 -m http.server 8085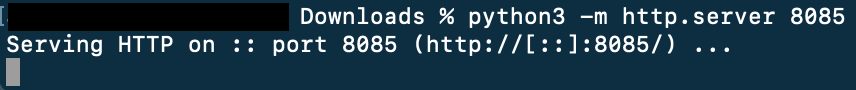
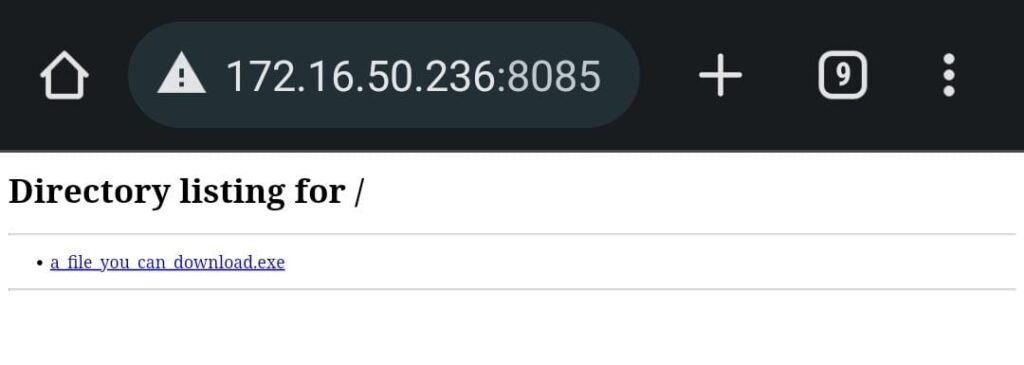
What this means? Your friend can now open http://<172.x.x.x>:8085 to access this computer and download files in your Downloads directory!
and get your Thapar Wifi Local Ip using:
ifconfig | grep “172”
for linux/mac-os
ipconfig | findstr /c:”172″
for windows
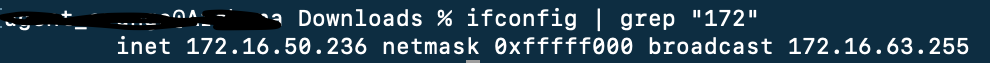
See? Note the IP address! (here 172.16.50.236) and give this to your friend! So he can access your files on this url!
http://172.16.50.236:8085
A note from the past
Ignore this part if you are not interested in listening to some fun facts and incidents I faced while doing this!
So first of all, It all started in the first semester of college, at that time, the LAN access was blocked. ie you cannot access other’s IPs and thus you were not able to do all these fun stuff (which you can right now), and I really don’t know what triggered the change that they removed the blockage on local network access and when could they enforce it again! But for now, we are all safe xD!
So coming back to the old topic, the thing is that my curiosity about networks led me to a simple fact in my first and second semester of university, that is the Thapar inter-lan connections are not possible, but after some research and experiments on different protocols and etc (Technical), I observed one thing. Even when the access was blocked, that was on conventional IPv4 addresses (ie 172.x.x.x), there were no such restrictions on IPv6 addresses (link-local, in the form of fe80:y:y:y:y:y:y:y), This led me to create the Holy altar of IPv6 Tunneling – xTIntranet. This was in 3rd semester of my University!
Now here’s the fun part – It took me 1 year (ie 2 semesters) and half a year (one semester) to reach this point. Where I made a fully flexible CLI (Command-line interface) to connect LANs on thapar wifi together! (ie you can access each other using IPv4 masked IPv6 addresses, so it was basically using IPv4 addresses but the communications were done using IPv6).
But guess what?
Within a week of the public release of this application (basically me advertising it and telling people how to use this), the LAN networks were opened (bruhhhh), ie IPv4 based communication in the local networks is not blocked anymore… (The network administration snapped their fingers and my whole work was destroyed. just like that)

Anyways, enough crying. Onto next part!
Revelation 2: VPN works, but with some catch!
Not gonna take credit for this one, this observation was not mine. It was thanks to my friend Raghav Tinker for telling me this trick one day! (Go follow his GitHub peeps)
So fundamentally, If you have ever tried using the wifi and going to some sites, You will see a Fortinet block page. Now Fortinet is a commercial-grade firewall to enforce site-blocking etc. It is so good that it also blocks major VPN providers and the usual method of using VPNs to bypass blocks might not even work. Before finding (or you can say making) this trick, I, with my other friends were forced to search for a working VPN and wasted a lot of time doing so. therefore I would like to present this trick!
Getting to the topic, essentially Fortinet also enforced port analysis and somehow identify packet-level data and cryptographic signatures to identify if someone is trying to connect to a VPN (which is blocked obviously), but one can use the unrestricted port 443 (Used for HTTPS) to connect to VPNs, basically, the port 443 is an exception from this deep packet analysis, as this is a common port for secure sites which they cannot entirely block! So using this trick you can try to find VPNs that connect using port 443, these VPNs have higher chances to work!
Even better, use Azpn (Azure Free VPN) as your free VPN solution
For those who don’t know Azpn is a tailor-made free VPN solution for Thapar Wifis. It uses the student id of students (@thapar.edu) to give them a free VPN profile which they can use for various purposes! I personally use this and am using this for half a year already, with no problems, high-stunning speeds, and ultra-low latency. You can even play games like Fortnite/Valorant etc on this.
Link to the project and my blog regarding the same:
Blog link (Start with this) – https://withme.skullzbones.com/blog/programming/self-hosted-free-vpn-using-azure-student-plan-with-edu-accounts-unblock-fortinet/
Github Repository – https://github.com/hari01584/Azpn-Azure-Free-VPN
Google Collab NB – https://colab.research.google.com/drive/1jrltUfshELXj_DDDriPMEB-f0oyh0qnh?usp=sharing
If you use this, do send me the reviews/feedback! (btw I am the creator of this thing so you can always call me for any help xD)
Revelation 3: We are not secure.
This is something I wouldn’t be showing you guys how to perform. but in a nutshell, It means that anyone using Thapar-Wifi is not secure and is vulnerable to a lot of attacks! this is especially so after the inter-lan connection blockage is removed! This is an in-direct consequence of our first revelation in this series (We are all Connected)
Some of you might not believe me, so here is one of the attacks.
Attack name – ARPSpoof and ARPInjection
Essentially if you ever heard of this term then you already know what I mean. but for the first-timers, Imma quickly copy-paste the meaning from google xD
In computer networking, ARP spoofing, ARP cache poisoning, or ARP poison routing, is a technique by which an attacker sends (spoofed) Address Resolution Protocol (ARP) messages onto a local area network. Generally, the aim is to associate the attacker’s MAC address with the IP address of another host, such as the default gateway, causing any traffic meant for that IP address to be sent to the attacker instead.
https://en.wikipedia.org/wiki/ARP_spoofing
ARP spoofing may allow an attacker to intercept data frames on a network, modify the traffic, or stop all traffic. Often the attack is used as an opening for other attacks, such as denial of service, man in the middle, or session hijacking attacks.[1]
The attack can only be used on networks that use ARP, and requires attacker have direct access to the local network segment to be attacked.[2]
How to do this?
Sorry, not gonna tell you. This was a blog post to reveal information about the thapar-wifi, not to encourage hacking! So due to ethical and obvious reasons, there won’t be any How-to tutorial for hacking others on thapar wifi in this! But any smart person could google arp spoofing attack and get all the resources with tutorials to do this. Very easy (and insecure as well).
A story of me hacking my friend to verify this
So this was a very CONSENTED attack on my friend (just a pun), basically, this friend is called A*****(name censored on his request) (Called A thereafter). The day I found the arp-spoof attack, I wanted to verify this, and make sure that it really is not something that is just one of the usual blunders. So I set up my HACKING MACHINE (again a pun) and called this friend A, Firstly I asked him to give me his local IP address, which he was very skeptical about, and didn’t give it to me even after requesting much (I asked him to give me the IP as I need to test something, which was true xD) failing to directly get his IP address I asked him to open a website (which I hosted myself, to get his local IP-address). Once I got the IP, I entered it into my HACKING MACHINE (again a pun) and started the interceptor program, after doing this I asked A (still on call), to open some website, and while he was doing this. I was able to see all websites he was trying to open and the data flowing between them. Obviously I could only do this for non-secure sites (HTTP) not HTTPS but still, this was something very surprising and also very fear-striking to be able to intercept data about anybody like that.
Again this was the last time I did it, and also told about my little hack-test to him afterward.
Ending Notes:
Had fun writing this but everything in here is just my observation and my thoughts on how things work and my research backing up my claim. that is to say that nothing written here is absolute and things could change over time. As of today (20th May 2022) everything written is up to the best of my knowledge, that is to say, I will try to do my best to update this blog post to reflect any changes that might happen in the unforeseen future! With that being said! Thank you for reading this all and having enough patience to read this all (Assuming you did). Also, I’m sorry for any grammatical mistakes, writing problems, etc that might be there in this blog (Blame Grammarly not me tho)


Hello
I need to
Wow, awesome blog format! How lengthy have you ever been running a blog for?
you made blogging glance easy. The entire look
of your web site is excellent, as smartly as the content material!
You can see similar: najlepszy sklep and here sklep internetowy